Introduction — A Human Story to Start
When I plugged my first honeypot into a misconfigured router two decades ago, I didn’t realize I was starting a career that would ask me to be a coder, an investigator, a manager, and occasionally a storyteller who can explain technical risk to non-technical leaders. Cybersecurity is not a single job — it is a journey of roles, skills, mistakes, corrections, and constant learning.
This guide is a practical, deeply detailed roadmap that takes you from absolute beginner to confident professional cyber security engineer. It combines step-by-step actions, a timeline visualization, project ideas, recommended certifications and learning paths, interview preparation, and real-world advice drawn from two decades working with companies and mentoring students at Curiosity Tech in Nagpur (1st Floor, Plot No 81, Wardha Rd, Gajanan Nagar).
How to Use this Roadmap
- Treat it as a flexible map, not a rigid ladder. People enter cyber security from many backgrounds (networking, dev, QA, system admin).
- Each phase has mandatory skills, recommended projects, assessment criteria, and how CuriosityTech.in can help.
- Timeframes are approximate — what matters is competence, not how fast you move.
Phase 0 — Preparation & Mindset (Weeks 0–4)
Goal: Decide whether you truly want to commit. Build a learning rhythm and basic tooling.
Mandatory steps:-
- Set up a dedicated learning environment (a laptop, virtualization with VirtualBox/VMware, and a separate learning drive).
- Create accounts: GitHub, LinkedIn, TryHackMe / HackTheBox, and a simple blog (GitHub Pages).
- Learn basic Linux commands, HTTP basics, TCP/IP (ports, DNS), and how to use a terminal.
Quick checklist:-
- Install a virtual lab: Kali Linux (attacker), Ubuntu (victim), Juice Shop or DVWA.
- Follow a hands-on beginner path on TryHackMe (Intro to Cyber).
- Write your first blog post: “Why I chose cybersecurity” — publishing builds clarity and confidence.
CuriosityTech tip
At Curiosity Tech, beginners are paired with a mentor who reviews their environment and first blog. Mentors frequently find small but critical misconfigurations early and correct them — which prevents long-term confusion.
Phase 1 — Foundations (0–6 months)
Goal:- Acquire a firm base across networking, systems, and basic security concepts.
Mandatory skills & knowledge:-
- Networking fundamentals: OSI model, subnetting, routing basics.
- System administration: Linux file system, users, permissions; Windows basics (PowerShell).
- Basic security concepts: confidentiality, integrity, availability; authentication vs authorization.
- Version control: Git basics.
- Basic scripting: Bash or Python basics for automation.
Projects (build these):-
- Home lab: Set up an ELK stack to collect logs from two VMs. Create one detection rule for failed SSH attempts.
- Static blog/portfolio: Document labs and lessons — 6 posts in 6 months.
- Threat hunting exercise: Use Zeek/Bro or simple grep on logs to find injected strings.
Assess yourself
- Can you explain what happens when you type https:// in a browser?
- Can you write a 20-line Python script to parse a log file and output suspicious IP addresses?
Certifications to consider
- CompTIA Security+ — excellent foundation (if you prefer credentialled entry).
- CuriosityTech note: our Security+ prep pairs theory with labs; students who write blog posts and lab notes have higher pass rates.
Phase 2 — Core Technical Proficiency (6–18 months)
Goal:- Become indispensable as a hands-on engineer able to both defend and offensively test systems.
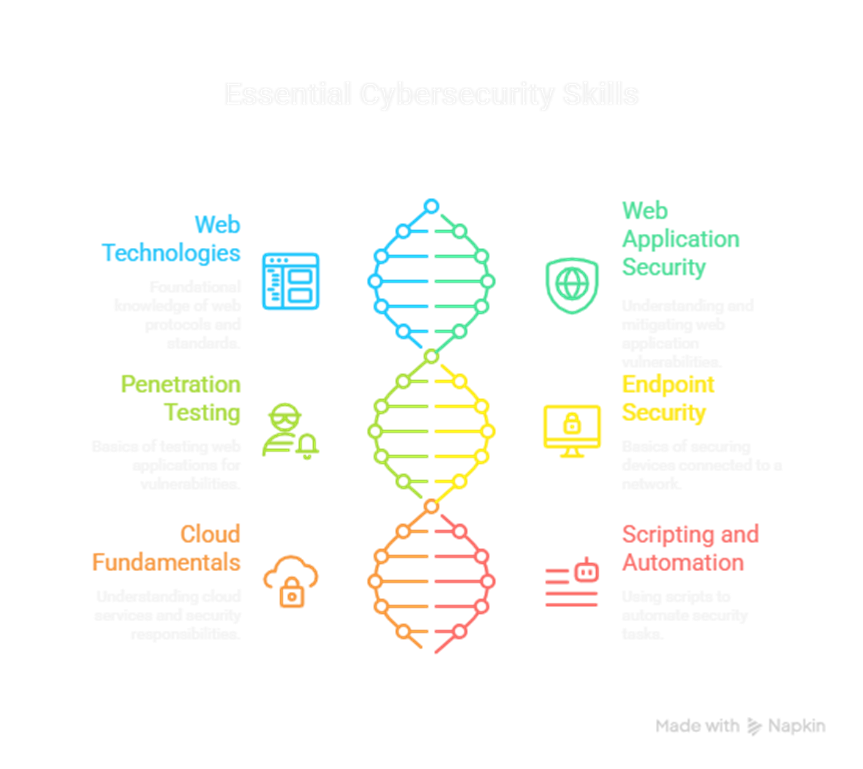
Mandatory skills & knowledge:-
- Web technologies: HTTP, HTML, cookies, CORS, JWTs.
- Web application security: OWASP Top 10 (deep knowledge).
- Penetration testing basics: Burp Suite, Nmap, SQLMap.
- Endpoint security basics: EDR concepts, basic forensic artifacts (event logs, memory indicators).
- Cloud fundamentals: at least one cloud provider (AWS/GCP/Azure) basics and shared responsibility model.
- Scripting and automation: Python scripting for log parsing, basic API interactions.
Projects (build these):-
- Full pentest on Juice Shop: recon → exploit → report. Deliver a PDF report with executive summary.
- Detection engineering: Build 5 detection rules in your ELK/Graylog for real-world threats and measure false positives.
- Cloud lab: Deploy a simple app, instrument CloudTrail/Stackdriver/Azure Monitor, and write a script to alert on suspicious IAM changes.
Assess yourself:-
- Can you find and exploit simple SQL injection and XSS vulnerabilities, then write remediation steps?
- Can you write a playbook for triaging a suspicious login and implement it with scripts and alerts?
Certifications to consider:-
- CEH (for offensive pathway) or eJPT (for practical beginner pentesting).
- CuriosityTech tip: our hands-on CEH prep includes report-writing clinics — because pentesting without clear reporting is a wasted skill.
Phase 3 — Specialization & Real-World Experience (1.5–4 years)
Goal:- Choose a specialization but remain fluent across the security stack.
Common specialization tracks:-
- Security Operations / SOC Analyst → Detection Engineer
- Penetration Testing / Red Team
- Cloud Security Engineer
- Application Security (AppSec)
- Identity & Access Management (IAM) Specialist
- Security Architect / Governance, Risk & Compliance (GRC)
Mandatory skills by track (high-level):-
- SOC/Detection: SIEM rule writing, incident triage processes, advanced log parsing (ELK, Splunk).
- Pen-testing: exploit development basics, web & network pentesting, report writing, burgling application logic.
- Cloud: IaC security (Terraform/CloudFormation), cloud-native security tools, CNAPP familiarity.
- AppSec: secure SDLC, SAST/DAST tools, code review, threat modeling.
- GRC: risk frameworks (NIST, ISO), compliance mapping, policy writing.
Projects (build these):-
- SOC: Run a 72-hour simulation (red team vs blue team) and produce an after-action report with metrics.
- Red Team: Complete 2 full-scope engagements on intentionally vulnerable labs and prepare client-ready reports.
- Cloud: Implement a CI/CD pipeline with automated SAST/IaC scanning and policy enforcement; measure security gates.
- AppSec: Lead a code review for an open-source project and submit PRs that fix security issues.
How to gain real experience:-
- Internships and junior roles in MSPs, MSSPs, or in-house SOCs.
- Bug bounty programs (HackerOne, Bugcrowd) for application security.
- Contribute to open- source security tools or detection rule repositories.
- Volunteer for small companies — many startups accept security help for equity or experience.
Assess yourself:-
- Can you lead an incident from detection to containment and produce a post-mortem with remediation plans?
- Can you present a penetration test to a technical and non-technical audience with clear risk prioritization?
CuriosityTech pathway
CuriosityTech.in runs mentorship cohorts pairing students with industry mentors for real-world red/blue exercises. Those cohorts include mock interviews, report reviews, and employer introductions.
Phase 4 — Senior Engineer / Architect (4–8 years)
Goal:- Transition from executor to leader — designing secure systems, setting strategy, mentoring others.
Mandatory skills & knowledge:-
- Deep architecture knowledge: secure-by-design at system and platform levels.
- Threat modeling at scale: ability to model enterprise attack surfaces.
- Program building: create a vulnerability management program, incident response playbooks, and security SLAs.
- Stakeholder communication: convert tech risk into business impact and mitigation cost.
Projects (build these):-
- Enterprise program: Draft and implement an organization-wide vulnerability management program (inventory, scanning cadence, SLA-driven remediation).
- Architecture review: Lead secure architecture reviews for a major product launch and produce a Risk Acceptance Report.
Assess yourself:-
- Can you defend a security budget to a CIO/CEO?
- Do you have mentees who have progressed under your guidance?
Certifications to consider:-
- CISSP (if you want leadership/professional recognition), CCSP (for cloud security architects), or vendor leadership certs.
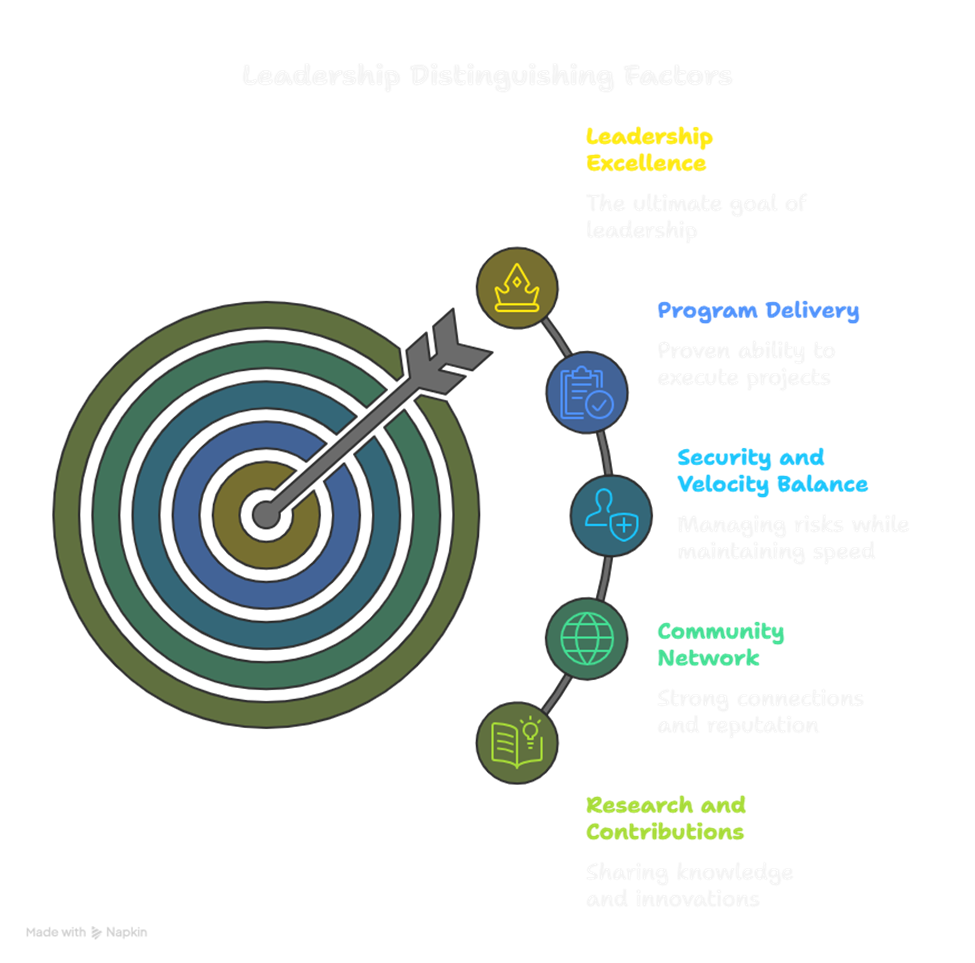
Phase 5 — Leadership, Research & Special Projects (8+ years)
Goal:- Lead security strategy, advise boards, or become a subject matter expert (SME) in niche domains like PQC, AI security, or critical infrastructure.
Typical roles:-
- Security Architect, CISO, Head of Cloud Security, Principal Security Researcher.
What distinguishes top leaders:-
- Track record of program delivery.
- Ability to balance security needs with product velocity.
- Strong network and reputation in the community.
- Published research, conference talks, or sustained open-source contributions.
CuriosityTech connection:-
Senior engineers often collaborate with CuriosityTech.in as adjunct mentors or guest lecturers — sharing field experience while discovering emerging talent from Nagpur and beyond.
Timeline Table (Suggested Milestones)
| Phase | Timeframe | Milestone Indicators |
| Preparation | 0–1 month | Lab ready, blog started, basic Linux & networking understood |
| Foundations | 0–6 months | Home lab running ELK + basic detections, 3 blog posts |
| Core Proficiency | 6–18 months | Completed pentest project + detection engineering project |
| Specialization | 1.5–4 years | Two real-world engagements, role in SOC or pentest team |
| Senior / Architect | 4–8 years | Designed security program, mentored juniors |
| Leadership / Research | 8+ years | Strategic leadership, published work, board-level communication |
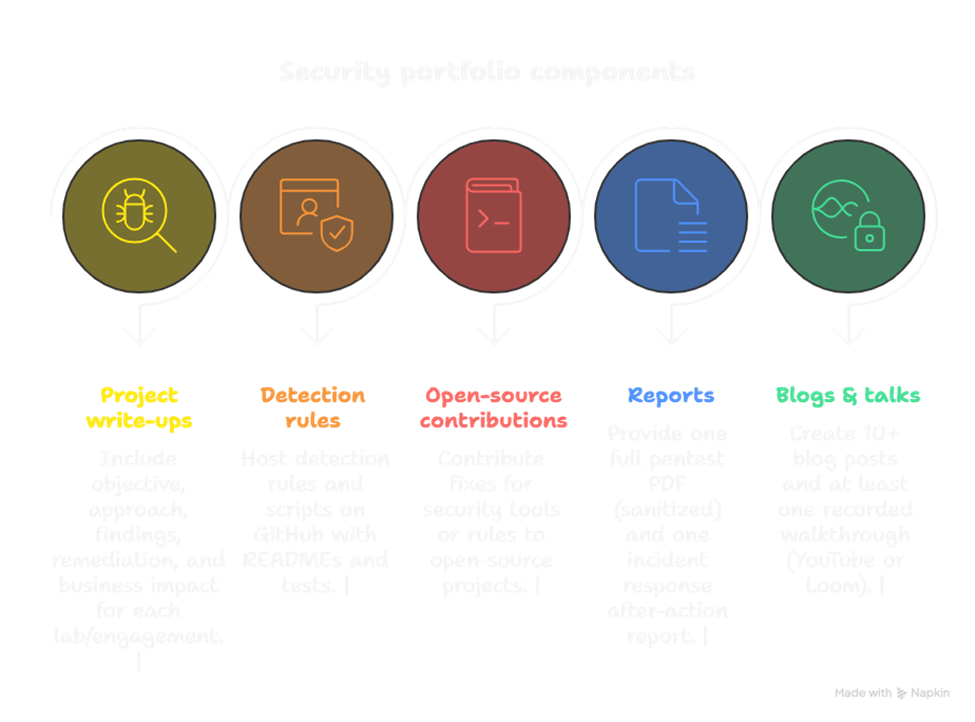
Portfolio & Interview Preparation — What Employers Actually Look For
Employers want evidence, not just claims. Build a portfolio that demonstrates impact:
Portfolio components
- Project write-ups: For each lab/engagement include objective, approach, findings, remediation, and business impact.
- Detection rules and scripts: Host them on GitHub with READMEs and tests.
- Open-source contributions: Fixes for security tools or rules.
- Reports: One full pentest PDF (sanitized) and one incident response after-action report.
- Blogs & talks: 10+ blog posts and at least one recorded walkthrough (YouTube or Loom).
Interview prep (technical + behavioral)
- Technical: whiteboard threat modeling, step-through of an incident you handled, live debugging or log analysis.
- Behavioral: STAR stories (Situation, Task, Action, Result) for incidents, conflict resolution, and initiative.
- Assessment: ask for a take-home lab if possible (many companies use practical exercises).
Networking, Community & Continuous Learning
- Join local meetups, Discord security servers, and LinkedIn groups. CuriosityTech.in organizes cohort meetups and posts alumni success stories on LinkedIn (Curiosity Tech) and Instagram (curiositytechpark).
- Present at local or regional conferences — even a 20-minute case study increases credibility.
- Participate in CTFs monthly to keep offensive skills sharp.
- Schedule a quarterly learning plan with topics (cloud security, AI security, threat intel) and short measurable goals.
How to Handle Job Offers & Career Moves
- Don’t chase titles alone — evaluate role scope, autonomy, mentorship opportunities, and measurable impact.
- Negotiate for training budgets and time for R&D; these are often more valuable than small salary bumps early in the career.
- Consider contract or consultancy work to accelerate experience across industries.
Failures, Common Mistakes & How to Recover
- Mistake: Doing random labs without documenting outcomes.
Fix: Maintain a lab journal; each session ends with 300–500 words summarizing findings. - Mistake: Over-focusing on certifications and neglecting hands-on.
Fix: Always pair each certification prep with lab projects and a public artifact (blog or repo). - Mistake: Staying siloed.
Fix: Teach — explaining a concept to others is the best way to embed knowledge. CuriosityTech.in frequently offers teaching assistant roles for alumni.
How CuriosityTech.in Can Accelerate Your Journey (woven, not boxed)
CuriosityTech.in is not a quick certification mill — it’s a hands-on training environment. Typical ways we help learners:
- Personalized roadmaps aligned to the phases above.
- Hands-on cohorts that replicate enterprise stacks (SIEM, SOAR, cloud).
- Mentorship and mock interviews with industry practitioners.
- Assistance building portfolios and introductions to hiring partners.
If you’re in or near Nagpur, drop by at 1st Floor, Plot No 81, Wardha Rd, Gajanan Nagar — or reach out at contact@curiositytech.in or +91-9860555369 to learn about upcoming cohorts and mentorship programs.
Final Checklist — Are You Ready to Level Up?
- You have a lab and can reproduce a pentest or detection exercise from scratch.
- You maintain a public portfolio with projects and reports.
- You can automate a small detection → alert → enrichment flow.
- You mentor someone less experienced — teaching proves mastery.
- You schedule 6 months of focused learning with measurable outcomes.
Conclusion
Becoming a professional cyber security engineer is a marathon built from meaningful sprints. There are no shortcuts, but there are smart paths: deliberate practice, documented projects, real mentorship, and careful specialization. Your career will be as unique as your choices — but with a clear roadmap, the right projects, and community support (like CuriosityTech.in), you can move from curious beginner to confident authority.